PRESS RELEASE: Hamburg, Germany – 06 September 2017 //
IoT security has become a major focus area for businesses, consumers and regulators. This focus is driven by the increasing number of IoT devices being connected to the internet and the new threats and attack vectors emerging almost on a daily basis. IoT Analytics, a leading provider of market insights and strategic business intelligence for Industry 4.0 and the Internet of Things (IoT), today published a 294-page IoT security report focusing on sizing the opportunity of the IoT security market for the period 2017 to 2022.
The report provide insights from the analysis done by the IoT Analytics analyst team who researched over 150 companies that offer IoT security technology solutions, reviewed 40+ implemented IoT security projects, undertook 25+ targeted industry interviews and attended several related conferences as part of the process.
Preview of some insights from the IoT security report
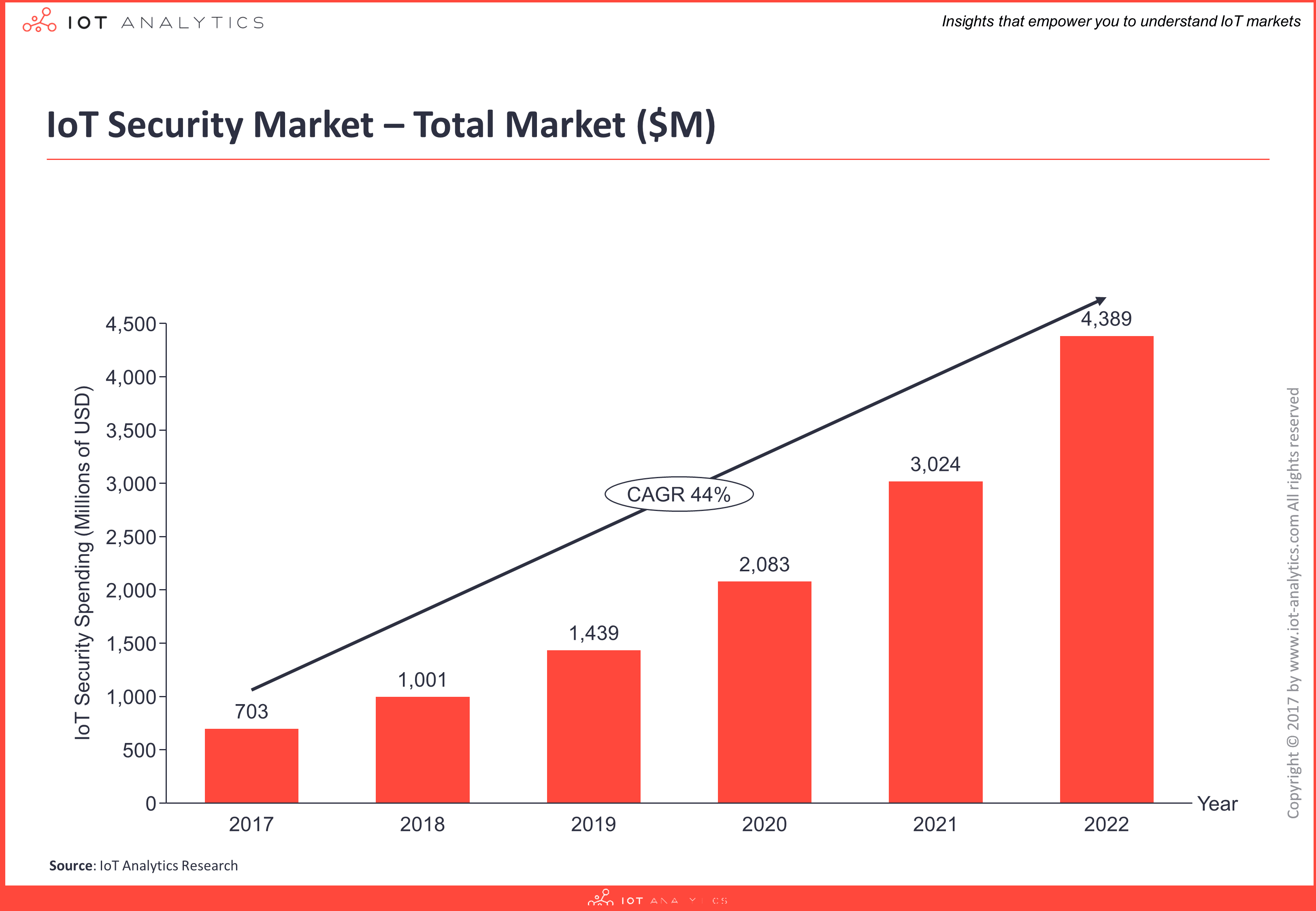
1. Global spending on IoT security is currently estimated at $703M for 2017 and forecasted to grow at a CAGR of 44% over the six-year period to become a $4.4B market opportunity by 2022 (Forecasts are based on the IoT security related revenue of leading technology companies in the field, across 12 industries and 21 technology areas).
2. The IoT security market is an aggregation of innovative startups and established firms such as global chip manufacturers, infrastructure providers, as well as cloud and enterprise software companies.
3. Cisco is the current market leader in the fragmented IoT security market with an estimated market share of 7%. The top 10 providers account for over 40% of the IoT security market.
What does the IoT security report contain?
1. The IoT security report contains a detailed breakdown of the market by solution type (software, hardware, services), by segment (12 industries), by solution provider (top 10 vendors), by technology (21 technology areas), and by region (7 regions).
2. The IoT security report also includes detailed company profiles of 10 large companies and 5 innovative smaller firms outlining their IoT security solutions, as well as an analysis of strategic partnerships and M&A activities.
3. An extensive IoT security segmentation is provided across 4 layers (device, communication, cloud, and lifecycle management) and 21 technology areas.
4. Five key implementation considerations are outlined for building secure IoT solutions, together with common best practices, an IoT security checklist and 8 detailed IoT security use cases presented in depth.
5. The IoT security report presents a comprehensive history of cyber security viruses (IT), cyber physical attacks (OT), IoT attacks and an evolution of cyber security solutions. Furthermore, today’s common threats in IoT are identified together with 5 types of IoT attackers and their motivation.
6. The report also includes a detailed excel database of 150 independent IoT Security vendors with extensive classification based on the vendor’s capabilities, estimated revenue, and industry focus across 60 sets of information.
Commenting on the report
Knud Lasse Lueth, Managing Director at IoT Analytics, said:
“Unfortunately lack of security is still a major concern for many people and enterprises that look to adopt IoT technology. Recent DDoS and ransomware attacks have made some technology users even more cautious than they already were. Therefore, IoT Security is one of the key topics any organization will have to master in the coming years in order to comfortably roll-out their IoT-based solutions. However, developing IoT solutions that are secure from device to cloud and everything in between, is extremely complex. Just one weak link can be taken advantage of by attackers to access the network. Our research addresses this complexity and aims to help firms overcome the challenges of building secure IoT solutions in any industry.”
Knud Lasse Lueth, MD at IoT Analytics
The IoT Security Report 2017-2022 is available for PURCHASE HERE or download a FREE SAMPLE HERE.
The IoT security market report is also available through our SUBSCRIPTION SERVICE giving members access to all content in our research stream.
For more on IoT security, check out our dedicated IOT SECURITY PAGE.
IoT Security Report – Companies mentioned (selected vendors only):
ARM, Atmel, Airbus Defence, Barracuda, Bastille Networks, Bayshore Networks, Cisco, ClearBlade, Comarch Technologies, Darktrace, Digicert, Device Authority, Dell, Endian, Forescout Technologies, Fortinet, Gemalto, HPE, IBM, Infineon Technologies, Intel, Juniper, Kaspersky Labs, Lightcyber, McAfee, Microsoft, Mocana, NXP, Palo Alto, Risucre, Rohde & Schwarz, SAP, Symantec, Thales e-Security, Utimaco, Venafi, WISeKey, Wurldtech (GE), ZingBox
IoT Security Report – Market Definition
For this market report, IoT security is defined as any element that protects Internet of Things solutions against virtual or physical damage on one or several of the following layers: device, communication, cloud and lifecycle management. For vendor analysis, the report only considers companies that offer independent IoT security products, not those that secure their own IoT platform or IoT solution in-house. To calculate the market size and individual company revenue, the report considers the revenues generated from the sales of security solutions including hardware, software, and services. Services is made up of professional services, consulting, implementation related services and managed services provided by the vendors. One should note, this report only looks at independent IoT security offerings available on the market and does not consider hobby developers/programmers that create their own security solutions.
Table of Contents – IoT Security Report
PREFACE: Current state of IoT security attacks
Executive Summary
1 IoT Security Overview
- 1.1. IoT Introduction
- 1.1.1 The 4 Major Layers of an IoT Solution
- 1.2. History of Cyber Security Viruses and Important Cyber Physical Breaches
- 1.2.1. Evolution of cyber security viruses (IT)
- 1.2.2. History of cyber physical attacks (OT)
- 1.2.3. History of IoT security attacks (IoT)
- 1.3. The History Evolution of Cyber Security Solutions
- 1.4. Today’s IoT Security Threats
- 1.4.1. General IoT attack surface
- 1.4.2. Common IoT threats
- 1.4.3. Types of IoT attackers
- 1.4.4. IoT attackers’ motivation
2 IoT Security Technology
- 2.1. Secure Device (Hardware)
- 2.1.1 Physical Security
- 2.1.2 Data at Rest (Device)
- 2.1.3 Chip Security
- 2.1.4 Secure Booting
- 2.1.5 Device Authentication
- 2.1.6 Device Identity Management
- 2.1.7 Further Principles for Device Security
- 2.2. Secure Communications (Network)
- 2.2.1 Access Management
- 2.2.2 Firewall / IPS / IDS
- 2.2.3 End-2-End Encryption
- 2.2.4 Further Principles for Secure Communication
- 2.3. Secure Cloud (Backend)
- 2.3.1 Data at Rest (Cloud) / DLP
- 2.3.2 Platform and Application Integrity Verification
- 2.3.3 Unified threat management
- 2.3.4 Further Principles for Secure Clouds
- 2.4. Secure Lifecycle Management
- 2.4.1 Risk Assessment
- 2.4.2 Policies & Auditing
- 2.4.3 Activity Monitoring
- 2.4.4 Updates & Patches
- 2.4.5 Vendor Control
- 2.4.6 User awareness assessment & training
- 2.4.7 Secure decommissioning
- 2.4.8 Further Principles for Secure Lifecycle Management
- 2.5. Constrained devices and the security implications
3 Market Analysis
- 3.1. Overall Market
- 3.2. Market Deep-Dives
- 3.2.1 By Solution Type
- 3.2.2 By Segment
- 3.2.3 By Solution Provider
- 3.2.4 By Technology
- 3.2.5 By Region
4 Competitive Landscape
- 4.1. Overview
- 4.2. 10 Large Vendors
- 4.3. 5 Innovative Smaller firms
- 4.4. Mergers and Acquisitions
- 4.5. Partnerships and Collaborations
- 4.6. 135 Selected Other Market Participants
5 Implementation Considerations
- 5.1. Assess IoT security gaps in the organization
- 5.2. Determine main responsibility for IoT security
- 5.3. Evaluate relevant standards, initiatives & guidelines
- 5.3.1. Global Security Initiatives
- 5.3.2. Industrial Focused Security Initiatives
- 5.3.3. Governmental Security Initiatives
- 5.4. Review the IoT environment security requirements
- 5.4.1. Secure technology stack
- 5.4.2. Security priorities
- 5.4.3. Secure data growth
- 5.4.4. Secure patching
- 5.5. Learn from existing IoT implementations
- 5.5.1. Security by design best practices and checklist
- 5.5.2. 8 Implementation projects
6 Market Trends
- 6.1. Market trends shaping IoT security (6)
Appendix
Target Audience
The focus of this IoT Security report is on industrial environments but the lessons learned can be leveraged by any organization looking to implement IoT Security. The IoT Security report may be most beneficial to OEMs looking into how to develop secure IoT solutions, technology vendors in the IoT & cyber security space. Also relevant for companies looking into M&A targets in the IoT Security area, as many Startups are mentioned.
About IoT Analytics
IoT Analytics is the leading provider of market insights & competitive intelligence for the Internet of Things (IoT), M2M, and Industry 4.0. The specialized data-driven research firm helps more than 40,000 Internet of Things decision-makers understand IoT markets every month. IoT Analytics tracks important data around the IoT ecosystem such as M&A activity, Startup funding, company projects, use cases and latest developments. Product offerings include in-depth market reports, technical whitepapers, sponsored research, regular newsletter, as well as Go2Market and consulting services. As a research pioneer, IoT Analytics combines traditional methods of market research such as interviews and surveys with state-of-the art web-mining tools to generate high-caliber insights.
IoT Analytics is headquartered in Hamburg, Germany.
For more information, visit www.iot-analytics.com.
Contact
For further comments or more information on this press release or the IoT Security report, please contact Stephanie Baumann, Public Relations Manager at IoT Analytics by emailing: press@iot-analytics.com.