In short
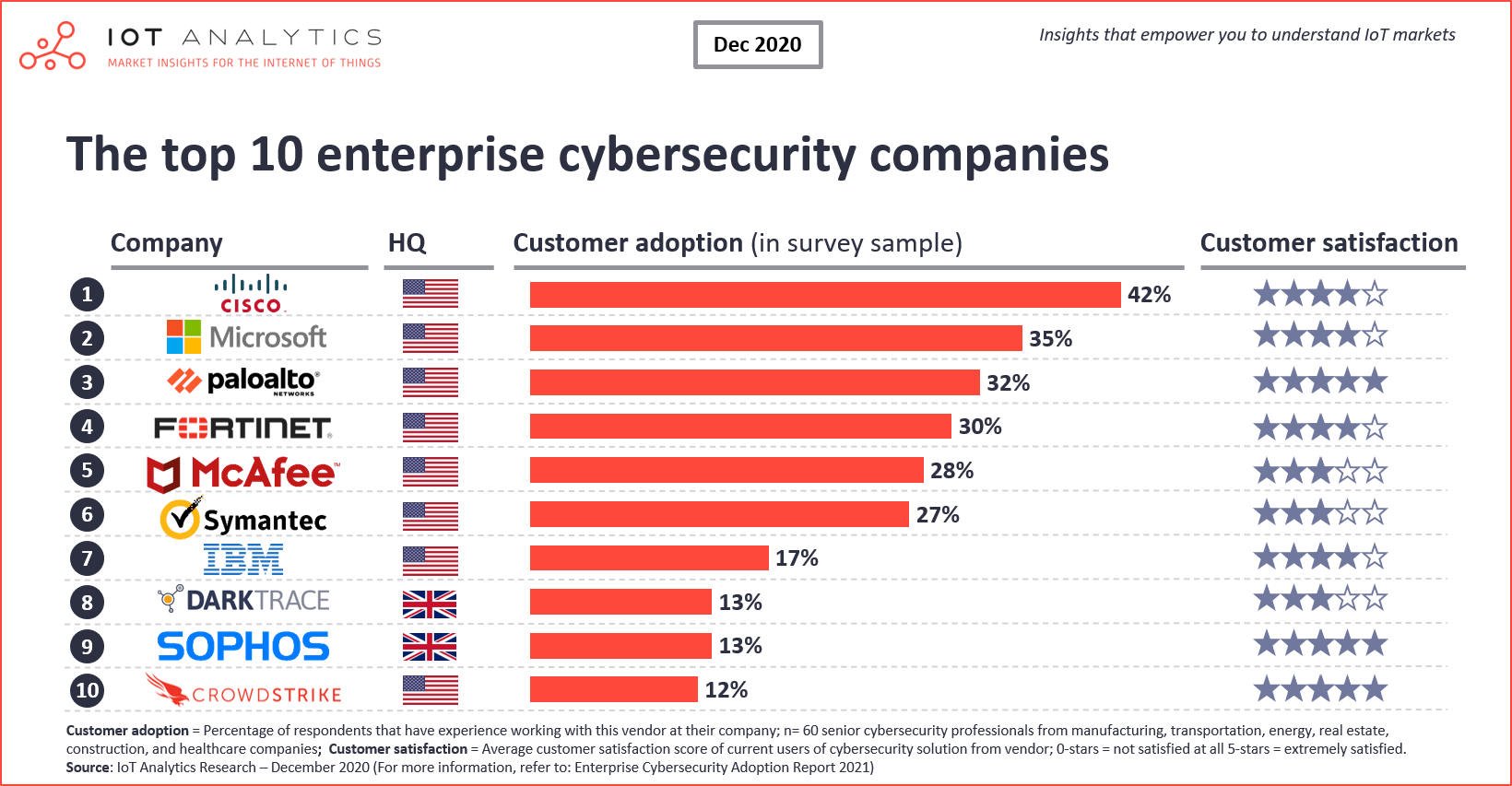
- Cisco, Microsoft, and Palo Alto Networks are the most popular enterprise cybersecurity companies
- IoT Analytics published a 120-page adoption report that identifies and analyzes 99 cybersecurity companies as well as other key adoption trends
- End-users are increasingly looking at cloud-based security as well as AI-based security solutions
Why it matters?
- Cyberattacks have been on the rise sharply throughout 2020
- Choosing the right cybersecurity company is crucial for success in mitigating cybersecurity risks
63% of companies reported an increase of cybersecurity attacks during the Covid-19 lockdown according to IoT Analytics latest cybersecurity research titled Enterprise Cybersecurity Adoption Report 2021. Notable cyber incidents in 2020 include the attack on the German software provider Software AG with the Clop ransomware and the attack on Japanese gaming giant Capcom. In the case of Software AG, attackers demanded more than $20 million ransom for personal employee information and confidential internal files. When the company declined, the attackers started to release confidential data.
The research, which is based on an extensive survey of cybersecurity decision makers, examines the top cybersecurity companies, among other things. 8 of the top 10 vendors are US-based with Cisco, Microsoft, and Palo Alto Networks topping the list of a total of 99 identified companies.
Cybersecurity company #1 Cisco
42% of surveyed respondents have experience working with Cisco as a cybersecurity company. This is the highest share amongst all cybersecurity companies. With more than 150 cybersecurity product families on offer today, Cisco arguably has one of the broadest security portfolios in the world. It allows the company to deliver end-2-end security, an aspect that was stressed as extremely important by respondents in the IoT Analytics research.
Earlier in 2020, Cisco consolidated all of its 83 individual cybersecurity brands under one brand called Cisco Secure which consists of 3 major product groups. The company also launched SecureX, a cloud-native, built-in platform that promises to put all the different security capabilities into one single place, thereby reducing complexity for the users.
Cybersecurity company #2 Microsoft
35% of respondents work with Microsoft to secure a parts of their IT or OT networks. A large portion of Microsoft’s cybersecurity offering is connected to Microsoft’s Azure cloud offering which is currently enjoying very strong adoption across enterprises. Examples include Azure Sentinel, a cloud-native SIEM, and Azure Security Center, a unified infrastructure security management system.
For IoT deployments, Azure Sphere is a unique approach with end-to-end security in mind. The solution consists of a security chip that acts as a hardware root of trust for IoT devices, runs the proprietary Azure Sphere operating and thereby enables a native, secure connectivity to the cloud with all typical security services such as device-to-cloud communication, threat detection, and lifecycle management.
Cybersecurity company #3 Palo Alto Networks
Palo Alto Networks is the third most used cybersecurity company. 32% of respondents stated that they use the California-based company’s services or products. It is worth noting that the satisfaction level of Palo Alto users was among the highest of all 99 identified vendors. Palo Alto Networks has been on a shopping spree in recent years. In 2019 and 2020 the firm acquired 8 other cybersecurity companies in order to complete its end-2-end offering. The most recent acquisition (November 2020) is the $800M purchase of Expanse, an attack surface management company. Among other things, the company prides itself at providing a complete inventory of their clients’ internet-connected assets. In line with Palo Alto’s strategic acquisition of Expanse, “establishing holistic asset transparency” also ranked among the top best-practices for IoT security in the IoT Analytics research.
Other notable findings from the research
- Companies, on average, have only deployed 12 out of 29 cybersecurity solutions. Of the 29 different cybersecurity solutions identified by IoT Analytics, the average surveyed organization has only fully rolled out 12 solutions, less than 50%. Hardware firewalls are the most common solution fully deployed.
- Crowdstrike, Sophos, and Palo Alto with highest overall satisfaction. Crowdstrike tops the list of cybersecurity companies in terms of overall satisfaction, followed by Palo Alto Networks, and Sophos.
- Cloud regarded as more secure than on-premise. The majority of respondents agree with the statements that “In general, a cloud set-up allows for better security than an on-premise set-up” (66%).
- AI/ML-based security solutions on the rise. 64% of companies are currently looking into the deployment of Artificial Intelligence /Machine Learning-based security solutions.
More information and further reading
Are you interested in learning more about cybersecurity?
The “Enterprise Cybersecurity Adoption Report 2021” is a 120-page report that analyses the deployment status of cybersecurity solutions, how vendors are rated, and what makes cybersecurity work. It is part of IoT Analytics’ ongoing coverage of “IoT software & platforms” as well as related and adjacent technologies.
This report provides answers to the following questions (among others):
- 9 most common cybersecurity threats and their assessment by end-users
- 29 cybersecurity solutions focusing on end-point security, network security and secure lifecycle management
- Insights on 99 vendors including satisfaction by region and industry
- Enterprise budget allocation & decision process (decision makers, information sources, selection criteria)
- Cybersecurity deep-dives: A. Security of the operations (OT) and B. Security of smart connected products
- Insights on cybersecurity priorities as a result of COVID-19
- Key success factors for making IoT security technologies work
- And more…
Sample:
The sample of the report provides a holistic overview of the available analyses (outline, key slides). The sample also provides additional context on the topic and describes the methodology of the research. You can download the sample here:
Related articles:
You may also be interested in the following recent article:
- The top 5 IT priorities for 2021
- 5 IoT security best practices to consider after the Covid-19 lockdown
Are you interested in continued IoT coverage and updates?
Subscribe to our newsletter and follow us on LinkedIn and Twitter to stay up-to-date on the latest trends shaping the IoT markets. For complete enterprise IoT coverage with access to all of IoT Analytics’ paid content & reports including dedicated analyst time check out Enterprise subscription.

